Computer Science Engineering - Online Test
Q1. Which of the following is/are example(s) of stateful application layer protocols?
(i) HTTP (ii) FTP (iii) TCP (iv) POP3
Answer : Option C
Explaination / Solution:
FTP and POP 3are stateful application layer protocols
Q2. Consider the C functions foo and bar given below:
int foo (int val ) {
int x = 0;
while (val > 0) {
x = x + foo ( val --);
}
return val ;
}
int bar (int val ) {
int x = 0;
while (val > 0) {
x = x + bar (val – 1) ;
}
return val ;
}
Invocations of foo (3) and bar (3) will result in:
Answer : Option B
Explaination / Solution:
Foo (3) calls foo (3) which in turn calls foo(3). This goes on infinite number of times which
causes memory overflow and causes abnormal termination.
Bar(3) → bar (2) →bar (1) →bar (0) (return 0) from here onwards bar (1) will call bar (0)
and bar (0) will return 0 to bar (1) & this goes on forever without causing memory overflow.
Q3. Assuming P ≠ NP, which of the following is TRUE?
Answer : Option B
Explaination / Solution:
If P!=NP, then it implies that no NP-Complete problem can be solved in polynomialtime
which implies that the set P and the set NPC are disjoint.
Q4. What is the Boolean expression for the output f of the combinational logic circuit
of NOR gates given below?
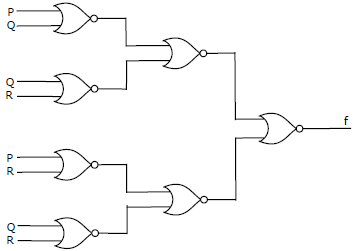
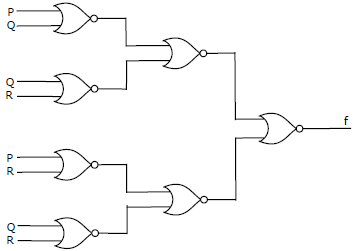
Answer : Option B
Explaination / Solution:
No Explaination.
Q5. Which of the following is/are undecidable?
1. G is a CFG. Is L (G) = Φ?
2. G is a CFG. IS L (G) = Σ*?
3. M is a Turning machine. Is L(M) regular?
4. A is a DFA and N is a NFA. Is L (A) = L (N) ?
Answer : Option D
Explaination / Solution:
There is an algorithm to check whether the given CFG is empty, finite or infinite and also to
convert NFA to DFA hence 1 and 4 are decidable
Q6. In the context of modular software design, which one of the following combinations is
desirable?
Answer : Option B
Explaination / Solution:
Cohesion is a measure of internal strength within a module, whereas coupling is a measure of
inter dependency among the modules. So in the context of modular software design there
should be high cohesion and low coupling.
Q7. A prime attribute of a relation scheme R is an attribute that appears
Answer : Option B
Explaination / Solution:
A prime attribute or key attribute of a relation scheme R is an attribute that appears in any of
the candidate key of R, remaining attributes are known as non-prime or non-key tribute
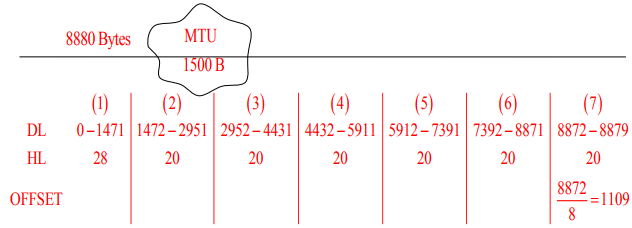
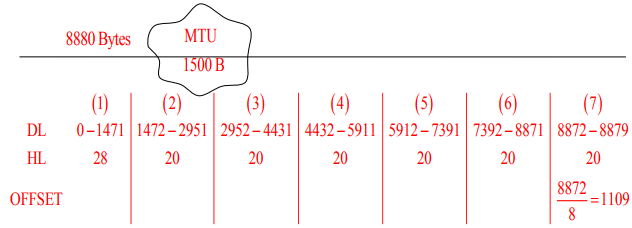
Q8. Host A sends a UDP datagram containing 8880 bytes of user data to host B over an Ethernet
LAN. Ethernet frames may carry data up to 1500 bytes (i.e. MTU = 1500 bytes). Size of UDP
header is 8 bytes and size of IP heard is 20 bytes.There is no option field in IP header How
many total number of IP fragments will be transmitted and what will be the contents of offset
field in the last fragment?
Answer : Option C
Explaination / Solution:
Q9. Consider the following two phase locking protocol. Suppose a transaction T accesses (for
read or write operations), a certain set of objects {O1, . . . , OK}. This is done in the following
manner:
Step 1. T acquires exclusive locks to O1, . . . , Ok in increasing order of their addresses.
Step 2. The required operations are performed.
Step 3. All locks are released.
This protocol will
Answer : Option A
Explaination / Solution:
2PL ensures serializability and here as we are following linear order in acquiring the locks
there will not be any deadlock.
Q10. The height of a tree is defined as the number of edges on the longest path in the tree. The
function shown in the pseudocode below is invoked as height (root) to compute the height of
a binary tree rooted at the tree pointer root.
int height (treeptr n)
{ if (n== NULL) return -1;
if (n → left == NULL)
if (n → right ==NULL) return 0;
else return BI ; // Box 1
else {h1 = height (n → left);
if (n → right == NULL) return (1+ h1);
else {h2 = height (n → right);
return B2 ; // Box 2
}
}
}
The appropriate expressions for the two boxes B1 and B2 are
Answer : Option A
Explaination / Solution:
No Explaination.