Computer Science Engineering - Online Test
Q1. Host A (on TCP/IP v4 network A) sends an IP datagram D to host B (also on TCP/IP V4
network B). Assume that no error occurred during the transmission of D. When D reaches B,
which of the following IP header field(s) may be different from that of the original datagram
D? (i) TTL (ii) Checksum (iii) Fragment Offset
Answer : Option D
Explaination / Solution:
While an IP Datagram is transferring from one host to another host, TTL, Checksum and
Fragmentation Offset will be changed.
Q2. Given below are some algorithms, and some algorithm design paradigms
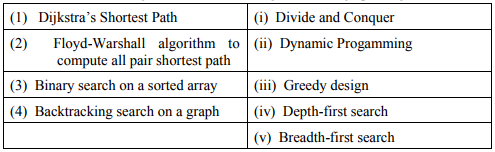
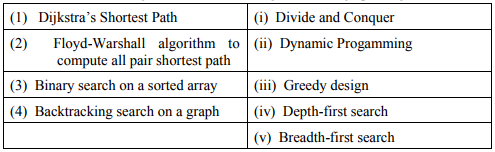
Match the above algorithms on the left to the corresponding design paradigm they follow.
Answer : Option C
Explaination / Solution:
Dijkstra shortest path algorithm find next node by choosing minimum distance hence greedy
approach.
Floyd warshall always apply dynamic programming, once it saves a cost and in the next
iteration it will change if this is minimum hence dynamic.
Binary search always divide on two parts .Hence divide and conquer.
Backtracking uses by DFS, one it will reach to dead end it will take back track.
Q3. An undirected graph G(V,E) contains n ( n > 2 ) nodes named v1, v2,....vn . Two
nodes vi, vj are connected if and only if 0 < |i − j| ≤ 2. Each edge (vi ,vj ) is
assigned a weight i + j. A sample graph with n = 4 is shown below
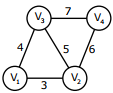
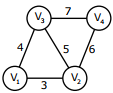
What will be the cost of the minimum spanning tree (MST) of such a graph with n
nodes?
Answer : Option B
Explaination / Solution:
No Explaination.
Q4. What is the correct translation of the following statement into mathematical logic?
“Some real numbers are rational”
Answer : Option C
Explaination / Solution:
Option A: There exists x which is either real or rational and can be both.
Option B: All real numbers are rational
Option C: There exists a real number which is rational.
Option D: There exists some number which is not rational or which is real.
Q5. Fetch_And_Add (X, i) is an atomic Read-Modify-Write instruction that reads the value of
memory location X, increments it by the value i, and returns the old value of X. It is used in
the pseudocode shown below to implement a busy-wait lock. L is an unsigned integer shared
variable initialized to 0. The value of 0 corresponds to lock being available, while any nonzero
value corresponds to the lock being not available.
AcquireLock(L){
While (Fetch_And_Add(L,1))
L = 1;
}
Release Lock(L){
L = 0;
}
This implementation
Answer : Option B
Explaination / Solution:
1. Acquire lock (L) {
2. While (Fetch_And_Add(L, 1))
3. L = 1.
}
4. Release Lock (L) {
5. L = 0;
6. }
Let P and Q be two concurrent processes in the system currently executing as follows
P executes 1,2,3 then Q executes 1 and 2 then P executes 4,5,6 then L=0 now Q executes 3 by which L will be set to 1 and thereafter no process can set
L to zero, by which all the processes could starve.
Q6. An index is clustered, if
Answer : Option C
Explaination / Solution:
Clustered index is built on ordering non key field and hence if the index is clustered then the
data records of the file are organized in the same order as the data entries of the index.
Q7. Consider a hard disk with 16 recording surfaces (0 - 15) having 16384 cylinders (0 - 16383)
and each cylinder contains 64 sectors (0 - 63) . Data storage capacity in each sector is 512
bytes. Data are organized cylinder–wise and the addressing format is . A file of size 42797 KB is stored in the disk and the starting disk location of the file is
<1200, 9, 40>. What is the cylinder number of the last sector of the file, if it is stored in a
contiguous manner?
Answer : Option D
Explaination / Solution:
42797 KB = (42797 × 1024)/512 = 85594 sectors
Starting is (1200,9,40) contains total 24 + (6×64)=408 sectors
Next, 1201, --------, 1283 cylinders contains total 1024×83 = 84992 sec tors
each cylinder contains 16×64 = 1024 sec tors)
Total = 408+84992 = 85400 sec tors
The required cylinder number is (1284) which will contain the last sector of the file
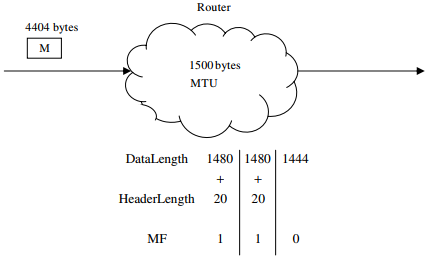
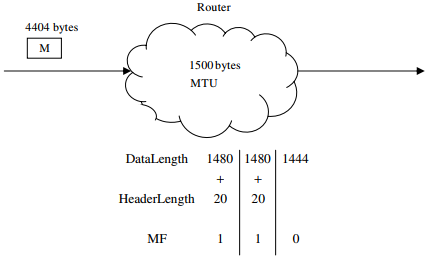
Q8. An IP router with a Maximum Transmission Unit (MTU) of 1500 bytes has received an IP
packet of size 4404 bytes with an IP header of length 20 bytes. The values of the relevant
fields in the header of the third IP fragment generated by the router for this packet are
Answer : Option A
Explaination / Solution:
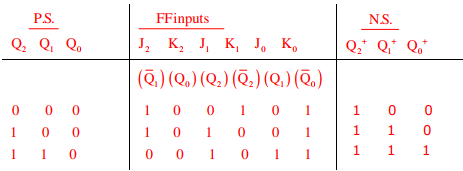
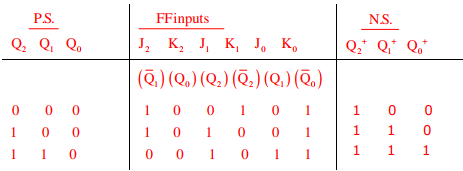
Q9. 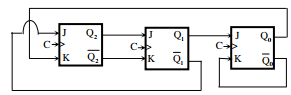
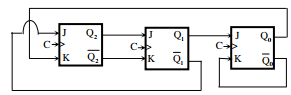
The above synchronous sequential circuit built using JK flip-flops is initialized with
Q2Q1Q0 = 000. The state sequence for this circuit for the next 3 clock cycles is
Answer : Option C
Explaination / Solution:
Q10. Suppose you are provided with the following function declaration in the C programming
language
int partition (int a [ ], int n);
The function treats the first element of a [ ] as a pivot, and rearranges the array so that all
elements less than or equal to the pivot is in the left part of the array , and all elements greater
than the pivot is in the right part. In addition, it moves the pivot so that the pivot is the last
elements of the left part. The return value is the number of elements in the left part.
The following partially given function in the C programming language is used to find the Kth smallest element in an array a [ ] of size n using the partition function We assume
k ≤ n.
int kth _smallest (int a [ ], int n, int k)
{
int left _ end = partition (a,n);
if (left _ end + 1 == k) {
return a [left _ end];
}
if (left _ end + 1 > k) {
return kth _ smallest (__________________);
}else {
return kth_smallest (_______________________);
}
}
The missing argument lists are respectively
Answer : Option A
Explaination / Solution:
No Explaination.