Computer Science Engineering - Online Test
Q1. A binary operation ⊕ on a set of integers is defined as x ⊕ y = x2 + y2. Which one of the
following statements is TRUE about ⊕?
Answer : Option A
Explaination / Solution:
x ⊕ y = x2 + y2 = y2 + x2 = y ⊕ x
∴ commutative
Not associative, since, for example
(1 ⊕ 2) ⊕ 3 ≠ 1 ⊕ (2 ⊕ 3)
Q2. A RAM chip has a capacity of 1024 words of 8 bits each (1K × 8) . The number of 2 × 4
decoders with enable line needed to construct a 16K × 16 RAM from 1K × 8 RAM is
Answer : Option B
Explaination / Solution:
RAM chip size = 1k × 8 [1024 words of 8 bits each]
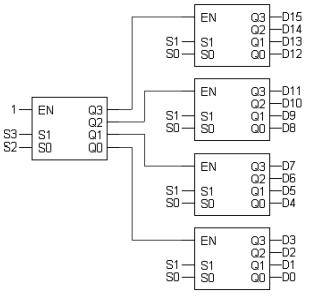
RAM to construct = 16k × 16
Number of chips required = (16k × 16)/(1k × 8) = 16 × 2 [16 chips vertically with each having 2 chips
horizontally]
So to select one chip out of 16 vertical chips, we need 4 x 16 decoder.
Available decoder is – 2 x 4 decoder
To be constructed is 4 x 16 decoder
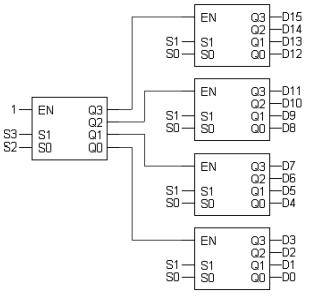
So we need 5, 2 x 4 decoder in total to construct 4 x 16 decoder.
Q3. Consider the following sequence of micro–operations
MBR ← PC
MAR ← X
PC ← Y
Memory ← MBR
Which one of the following is a possible operation performed by this sequence?
Answer : Option D
Explaination / Solution:
PC content is stored in memory via MBR and PC gets new address from Y. It represents a
function call (routine), which is matching with interrupt service initiation
Q4. In the following pairs of OSI protocol layer/sub-layer and its functionality, the
INCORRECT pair is
Answer : Option B
Explaination / Solution:
(a) One of the main functionality of Network Layer is Routing. So Option (a) is CORRECT.
(b) Bit Synchronization is always handled by Physical Layer of OSI model but not Data Link
Layer. So
Option (b) is INCORRECT.
(c) End – to – End Process Communication is handled by Transport Layer. So Option (c) is
CORRECT.
(d) MAC sub layer have 3 types of protocols (Random, Controlled and Channelized Access).
Q5. An unordered list contain n distinct elements. The number of comparisons to find an element
in this list that is neither maximum nor minimum is
Answer : Option D
Explaination / Solution:
Consider first three element of the list, atleast one of them will be neither minimum nor
maximum
ϴ(1)
Q6. We are given a set of n distinct elements and an unlabeled binary tree with n
nodes. In how many ways can we populate the tree with the given set so that it
becomes a binary search tree?
Answer : Option D
Explaination / Solution:
No Explaination.
Q7. Given the language L-{ab, aa, baa}, which of the following strings are in L*?
1) abaabaaabaa
2) aaaabaaaa
3) baaaaabaaaab
4) baaaaabaa
Answer : Option C
Explaination / Solution:
L ={ab, aa, baa}
Let S1 = ab , S2 = aa and S3 =baa
abaabaaabaa can be written as S1S2S3S1S2
aaaabaaaa can be written as S1S1S3S1
baaaaabaa can be written as S3S2S1S2
Q8. A process executes the code
fork ();
fork ();
fork ();
The total number of child processes created is
Answer : Option C
Explaination / Solution:
If fork is called n times, there will be total 2n running processes including the parent process.
So, there will be 2n -1 child processes.
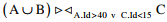
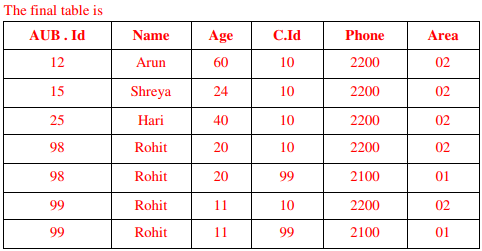
Q9. Consider the following relations A, B and C: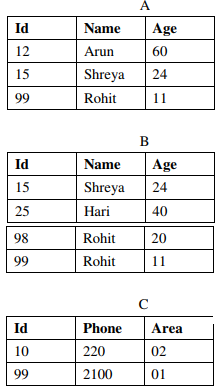
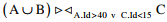
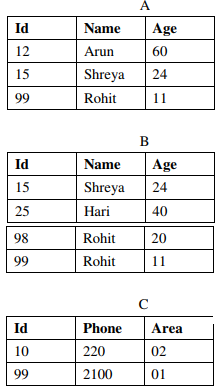
How many tuples does the result of the following relational algebra expression contain?
Assume that the schema of A ∪ B is the same as that of A.
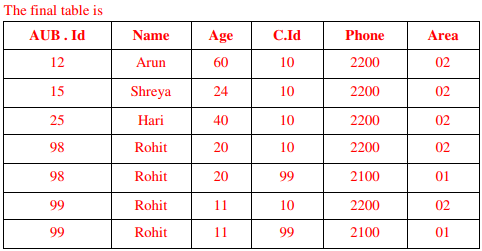
Answer : Option A
Explaination / Solution:
Q10. Which one of the following is NOT logically equivalent to ¬∃x (∀y (α) ∧ ∀z (β))?
Answer : Option A
Explaination / Solution:
No Explaination.