Information Technology - Online Test
Q1. A multilevel page table is preferred in comparison to a single level page table for translating virtual
address to physical address because
Answer : Option B
Explaination / Solution:
No Explaination.
Q2. The running time of an algorithm is represented by the following recurrence relation:
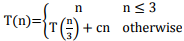
Which one of the following represents the time complexity of the algorithm?
Answer : Option A
Explaination / Solution:
No Explaination.
Q3. The keys 12, 18, 13, 2, 3, 23, 5 and 15 are inserted into an initially empty hash table of length 10 using
open addressing with hash function h(k) = k mod 10 and linear probing. What is the resultant hash
table?
Answer : Option C
Explaination / Solution:
No Explaination.
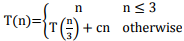
Q4. Let R and S be relational schemes such that R={a, b, c} and S={c}. Now consider the following queries
on the database:
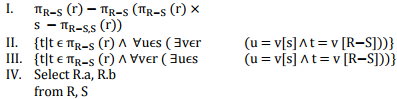
Where R.c = S.c
Which of the above queries are equivalent?
Answer : Option C
Explaination / Solution:
No Explaination.
Q5. P is a 16-bit signed integer. The 2’s complement representation of P is (F87B)16.
The 2’s complement representation of 8*P is
Answer : Option A
Explaination / Solution:
No Explaination.
Q6. Consider different activities related to email.
m1: Send an email from a mail client to a mail server
m2: Download an email from mailbox server to a mail client
m3: Checking email in a web browser
Which is the application level protocol used in each activity?
Answer : Option C
Explaination / Solution:
Sending an email will be done through user agent and message transfer agent by
SMTP, downloading an email from mail box is done through POP, checking email
in a web browser is done through HTTP
Q7. Consider the following intermediate program in three address code
p = a - b
q = p *c
p = u * v
q = p + q
Which one of the following corresponds to a static single assignment form of the above code
?
Answer : Option B
Explaination / Solution:
No Explaination.
Q8. Match all items in Group I with correct options from those given in Group 2
Group 1 Group 2
P. Regular expression 1. Syntax analysis
Q. Pushdown automata 2. Code generation
R. Dataflow analysis 3. Lexical analysis
S. Register allocation 4. Code Optimization
Codes:
Answer : Option B
Explaination / Solution:
No Explaination.
Q9. Consider the following graph:


Which of the following is NOT the sequence of edges added to the minimum spanning tree using
Kruskal’s algorithm?
Answer : Option D
Explaination / Solution:
No Explaination.
Q10. In quick sort, for sorting n elements, the (n/4)th the smallest element is selected as pivot using an O(n)
time algorithm. What is the worst case time complexity of the quick sort?
Answer : Option B
Explaination / Solution:
No Explaination.