Computer Networks - Online Test
Q1. Which one of the following hash functions on integers will distribute keys most uniformly
over 10 buckets numbered 0 to 9 for i ranging from 0 to 2020?
Answer : Option B
Explaination / Solution:
If we take first 10 elements, number of collisions taken by the hash function given by option
(B) is less when compared to others.
Q2. Assume that the bandwidth for a TCP connection is 1048560 bits/sec. Let α be the value of RTT in milliseconds. (rounded off to the nearest integer) after which the TCP window scale option is needed. Let β be the maximum possible window size the window scale option. Then the values of α and β are
Answer : Option C
Explaination / Solution:
No Explaination.
Q3. Which one of the following protocols is NOT used to resolve one form of address to another
one?
Answer : Option C
Explaination / Solution:
Except DHCP, remaining all the protocols are used to resolve one form of address to another
one.
Q4. Which of the following is/are example(s) of stateful application layer protocols?
(i) HTTP (ii) FTP (iii) TCP (iv) POP3
Answer : Option C
Explaination / Solution:
FTP and POP 3are stateful application layer protocols
Q5. Consider the following two phase locking protocol. Suppose a transaction T accesses (for
read or write operations), a certain set of objects {O1, . . . , OK}. This is done in the following
manner:
Step 1. T acquires exclusive locks to O1, . . . , Ok in increasing order of their addresses.
Step 2. The required operations are performed.
Step 3. All locks are released.
This protocol will
Answer : Option A
Explaination / Solution:
2PL ensures serializability and here as we are following linear order in acquiring the locks
there will not be any deadlock.
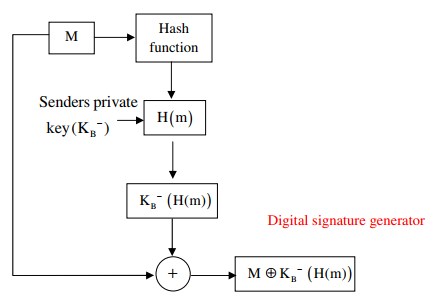
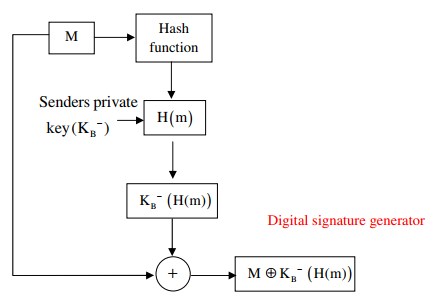
Q6. Consider that B wants to send a message m that is digitally signed to A. Let the pair of private
and public keys for A and B be denoted by  for x = A, B, respectively. Let Kx(m)
represent the operation of encrypting m with a key Kx and H (m) represent the message
digest. Which one of the following indicates the CORRECT way of sending the message m
along with the digital signature to A?
for x = A, B, respectively. Let Kx(m)
represent the operation of encrypting m with a key Kx and H (m) represent the message
digest. Which one of the following indicates the CORRECT way of sending the message m
along with the digital signature to A?
 for x = A, B, respectively. Let Kx(m)
represent the operation of encrypting m with a key Kx and H (m) represent the message
digest. Which one of the following indicates the CORRECT way of sending the message m
along with the digital signature to A?
for x = A, B, respectively. Let Kx(m)
represent the operation of encrypting m with a key Kx and H (m) represent the message
digest. Which one of the following indicates the CORRECT way of sending the message m
along with the digital signature to A?
Answer : Option B
Explaination / Solution:
Q7. A sender S sends a message m to receiver R, which is digitally signed by S with its
private key. In this scenario, one or more of the following security violations can take
place.
I. S can launch a birthday attack to replace m with a fraudulent message.
II. A third party attacker can launch a birthday attack to replace m with a fraudulent
message.
III. R can launch a birthday attack to replace m with a fraudulent message.
Which of the following are possible security violations?
Answer : Option B
Explaination / Solution:
Sender can launch a Birthday Attack to replace with fraudulent message, because he has the
signature and he can decrypt the signature by his own public key and gets the hash value.
With that same hash value, he can create another message and can be sent instead of original.
Hence option(B) is correct.
Q8. Consider a TCP client and a TCP server running on two different machines. After completing
data transfer, the TCP client calls close to terminate the connectional and a FIN segment is
sent to the TCP server. Server-side TCP responds by sending an ACK which is received by
the client-side TCP. As per the TCP connections state diagram (RFC 793), in which state does
the client-side TCP connection wait for the FIN from the sever-side TCP?
Answer : Option D
Explaination / Solution:
No Explaination.
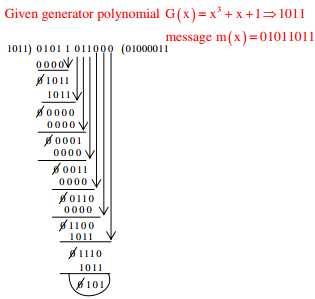
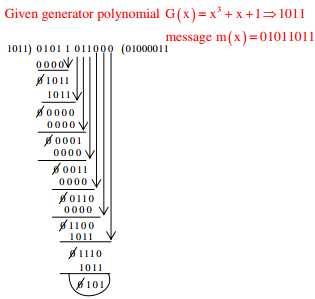
Q9. A computer network uses polynomials over GF(2) for error checking with 8 bits as
information bits and uses x3 + x + 1 as the generator polynomial to generate the check bits. In
this network, the message 01011011 is transmitted as
Answer : Option C
Explaination / Solution:
Q10. One of the header fields in an IP datagram is the Time to Live (TTL) field. Which
of the following statements best explains the need for this field?
Answer : Option B
Explaination / Solution:
No Explaination.